QuadRF: 4-Element Beamforming SDR Tile Coming to Crowd Supply
Back in January, we posted about open.space and their mission to unlock affordable open source earth-moon-earth (EME) bounce communications for the amateur radio public. Recently, we've seen that the project has been renamed to ScaleRF, with the EME system renamed to MoonRF, and the invisual tile renamed to QuadRF. They've also put out a new update post with a lot of interesting information and demonstrations. In the latest update, they also announced that the QuadRF 4-element tile will soon come to Crowd Supply for crowdfunding.
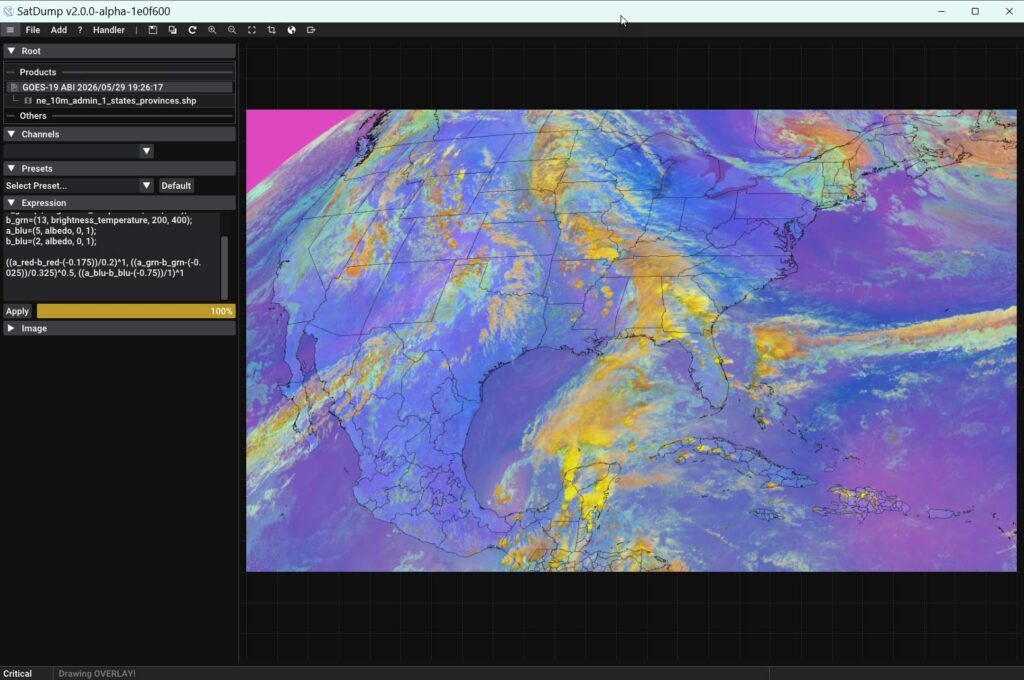
MoonRF is a software-defined radio-based tiling system that enables users to easily create large phased arrays by combining multiple smaller 'QuadRF' tiles consisting of four tile elements, a custom SDR, and a built-in Raspberry Pi 5. Although the ultimate goal is to produce a large system capable of working EME bounce communications, they show that a single QuadRF tile has considerable utility on its own.
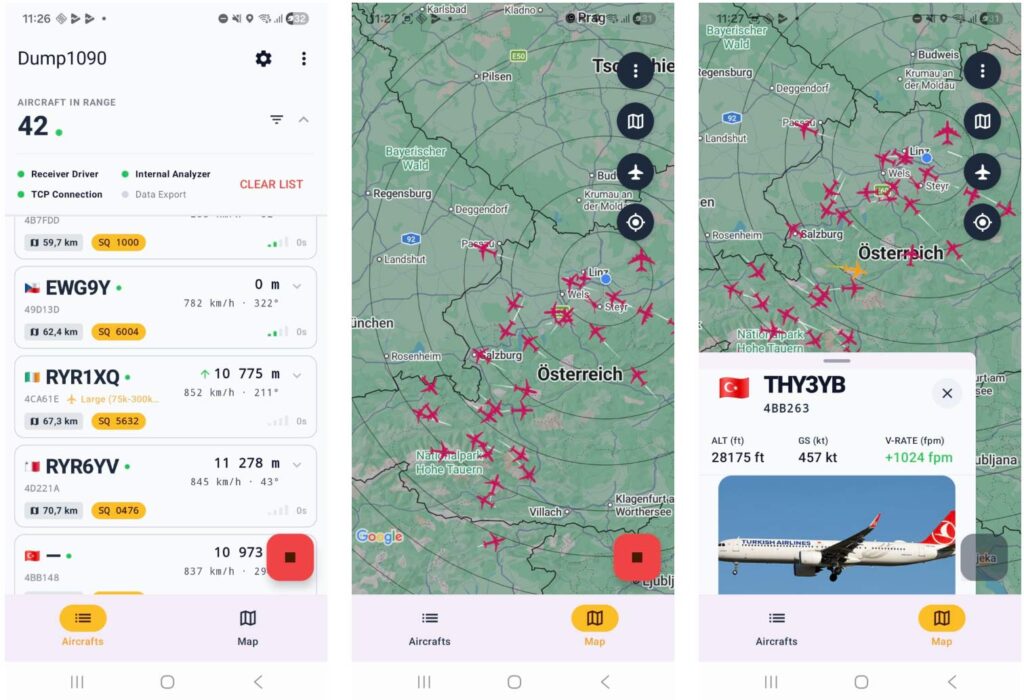
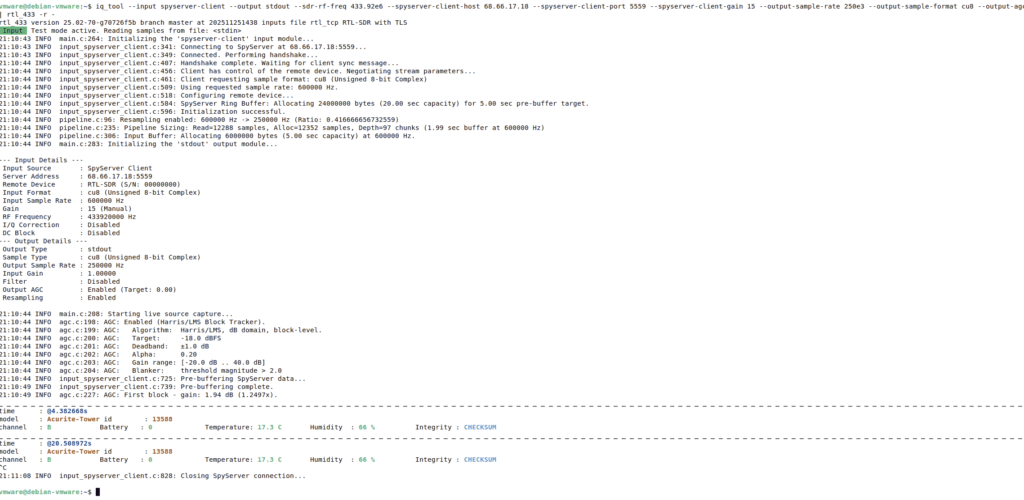
An interesting application they show is the ability to visualize and track RF signals using a single QuadRF and their augmented-reality smartphone app. QuadRF appears to be limited to the C-band (4.9–6.0 GHz), but many modern devices, such as smartphones and drones, operate at these frequencies, and in the video, they are able to track these devices with perfect accuracy.
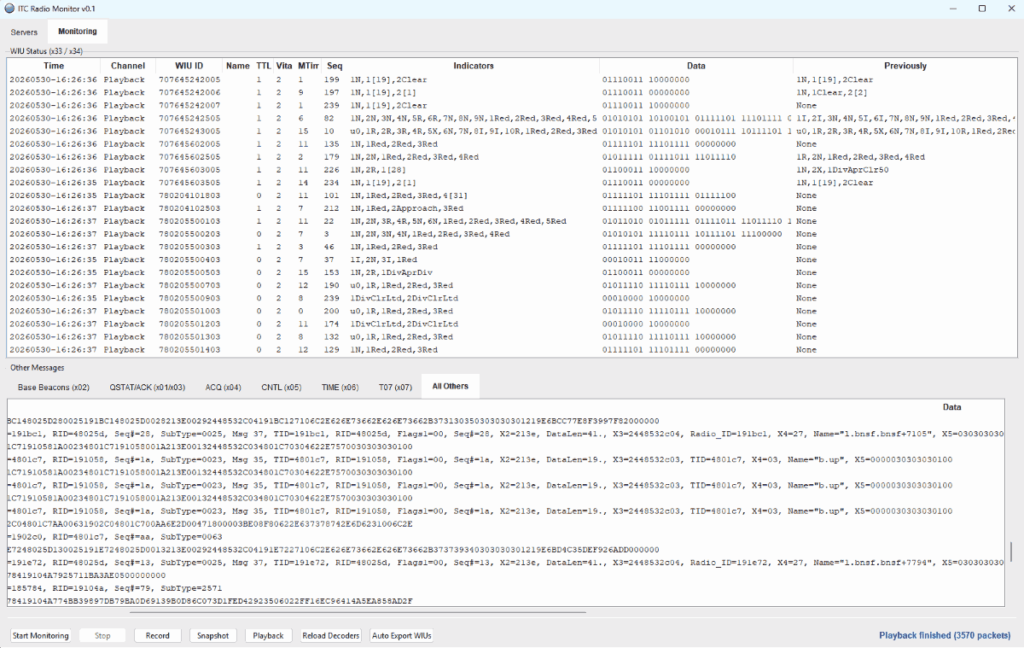
They also show that QuadRF has built-in web browser access to various programs, including a wireless camera decoder for drones.