Running a Tesla Model 3 on Autopilot off the Road with GPS Spoofing
Regulus is a company that deals with sensor security issues. In one of their latest experiments they've performed GPS spoofing with several SDRs to show how easy it is to divert a Tesla Model 3 driving on autopilot away from it's intended path. Autopilot is Tesla's semi-autonomous driving feature, which allows the car to decide it's own turns and lane changes using information from the car's cameras, Google Maps and it's Global Navigation Satellite System (GNSS) sensors. Previously drivers had to confirm upcoming lane changes manually, but a recent update allows this confirmation to be waived.
The Regulus researchers noted that the Tesla is highly dependent on GNSS reliability, and thus were able to use an SDR to spoof GNSS signals causing the Model 3 to perform dangerous maneuvers like "extreme deceleration and acceleration, rapid lane changing suggestions, unnecessary signaling, multiple attempts to exit the highway at incorrect locations and extreme driving instability". Regarding exiting at the wrong location they write:
Although the car was a few miles away from the planned exit when the spoofing attack began, the car reacted as if the exit was just 500 feet away— slowing down from 60 MPH to 24 KPH, activating the right turn signal, and making a right turn off the main road into the emergency pit stop. During the sudden turn the driver was with his hands on his lap since he was not prepared for this turn to happen so fast and by the time he grabbed the wheel and regained manual control, it was too late to attempt to maneuver back to the highway safely.
In addition, they also tested spoofing on a Model S and found there to be a link between the car's navigation system and the automatically adjustable air suspension system. It appears that the Tesla adjusts it's suspension depending on the type of road it's on which is recorded in it's map database.
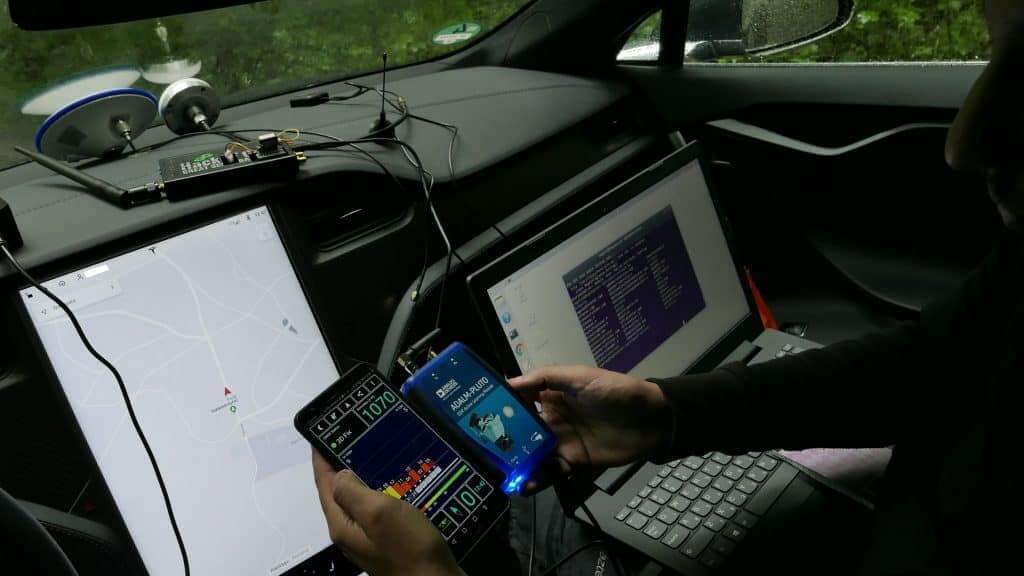
In their work they used a ADALM PLUTO SDR ($150) for their jamming tests, and a bladeRF SDR ($400) for their spoofing tests. Their photos also show a HackRF.
Regulus are also advertising that they are hosting a Webinar on July 11, 2019 at 09:00PM Jerusalen time. During the webinar they plan to talk about their Tesla 3 spoofing work and release previously unseen footage.
GPS/GNSS spoofing is not a new technique. In the past we've posted several times about it, including stories about using GPS spoofing to cheat at Pokémon Go, misdirect drivers using Google Maps for navigation, and even a story about how the Russian government uses GPS spoofing extensively.